The Problem
Security reviews are a bottleneck. Developers push code faster than reviewers can audit it, and when reviews do happen, they’re inconsistent — what one reviewer catches, another misses. Vulnerabilities slip into production not because people don’t care, but because the process doesn’t scale.
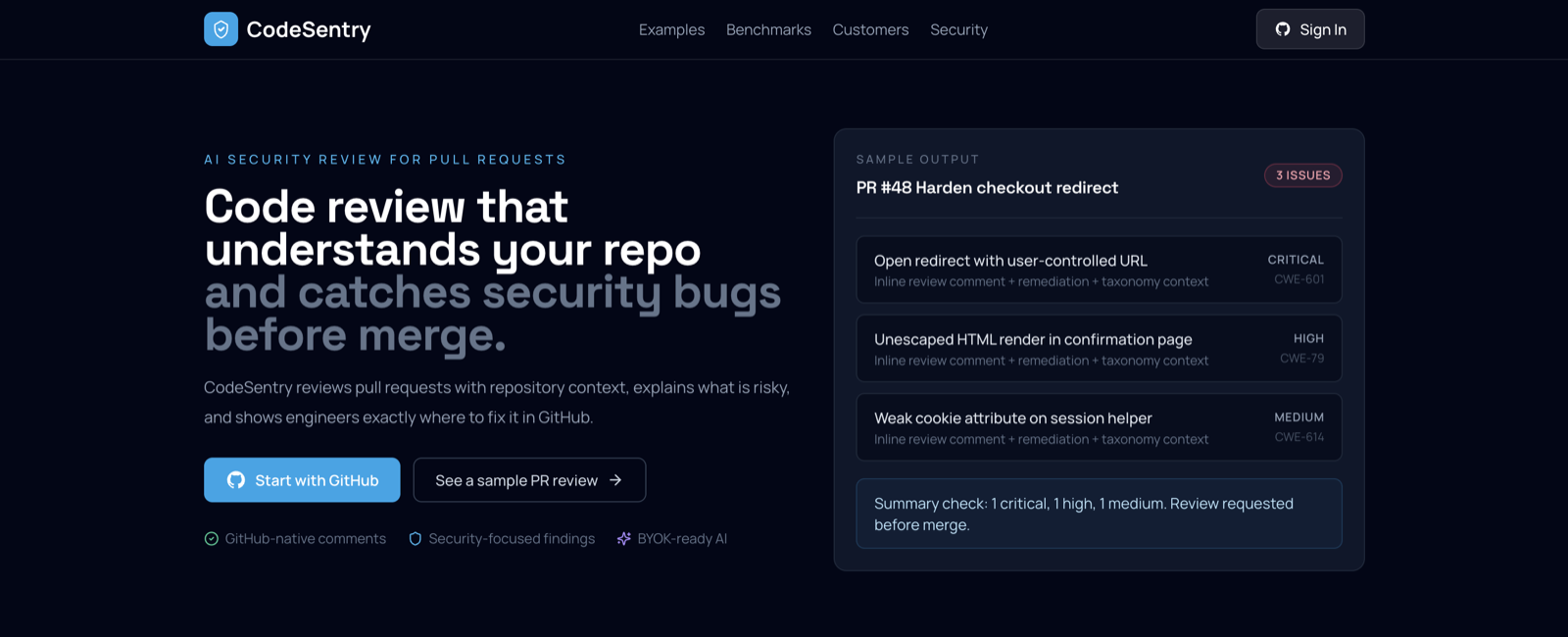
What CodeSentry Does
CodeSentry is a GitHub-integrated platform that automatically analyzes every pull request for security vulnerabilities. Install as a GitHub App — no CI config, no YAML, no pipeline changes. Open a PR, and CodeSentry reviews it.
Every finding carries multi-taxonomy mappings: CWE, OWASP Top 10, MITRE ATT&CK, and CAPEC identifiers — traceable classifications that map directly to compliance frameworks.
Analysis Pipeline
GitHub PR Webhook
│
▼
┌─────────────────────────────────────────────┐
│ Tier 1 — Regex Pattern Matching │
│ 35 rules · CWE Top 25 · < 100ms │
└──────────────────┬──────────────────────────┘
│
▼
┌─────────────────────────────────────────────┐
│ Tier 2 — Semgrep AST Analysis │
│ 25 rules · Taint tracking · 2-5s per file │
└──────────────────┬──────────────────────────┘
│
▼
┌─────────────────────────────────────────────┐
│ Deduplication & Clustering │
│ Merge overlapping findings from both tiers │
└──────────────────┬──────────────────────────┘
│
▼
PR Comment with line-level annotations
Architecture
Four services working together:
| Service | Stack | Role |
|---|---|---|
| Frontend | React + Vite | Dashboard, OAuth login, analysis reports |
| API Service | Node.js | Webhook ingestion, orchestration, REST APIs |
| Analysis Service | Python / FastAPI | Security rule engine (regex + Semgrep) |
| GitHub Service | Node.js | App auth, PR file fetching, review posting |
Data layer: PostgreSQL for findings, analysis runs, and repositories. Redis for ephemeral caching.
Coverage
35 CWE patterns across major vulnerability classes:
- Injection — SQL, Command, Code, NoSQL, LDAP, Template
- XSS — Reflected, Stored, DOM-based
- Broken Access Control — Path traversal, IDOR
- Cryptographic Failures — Weak algorithms, hardcoded keys
- Secrets — API keys, tokens, credentials in source
- SSRF — Server-side request forgery
- Deserialization — Unsafe object handling
- XXE — XML external entity processing
- Race Conditions — TOCTOU vulnerabilities
- Memory Safety — Buffer overflows, integer overflow
Plus 11 dependency risk patterns for known vulnerable package versions.