The Problem
The A2A (Agent-to-Agent) protocol gives agents a standard way to talk to each other — but the spec is transport, not security. Any agent that exposes an A2A endpoint is reachable by any caller. There’s no built-in concept of who gets to call what, with what permissions, or under what conditions.
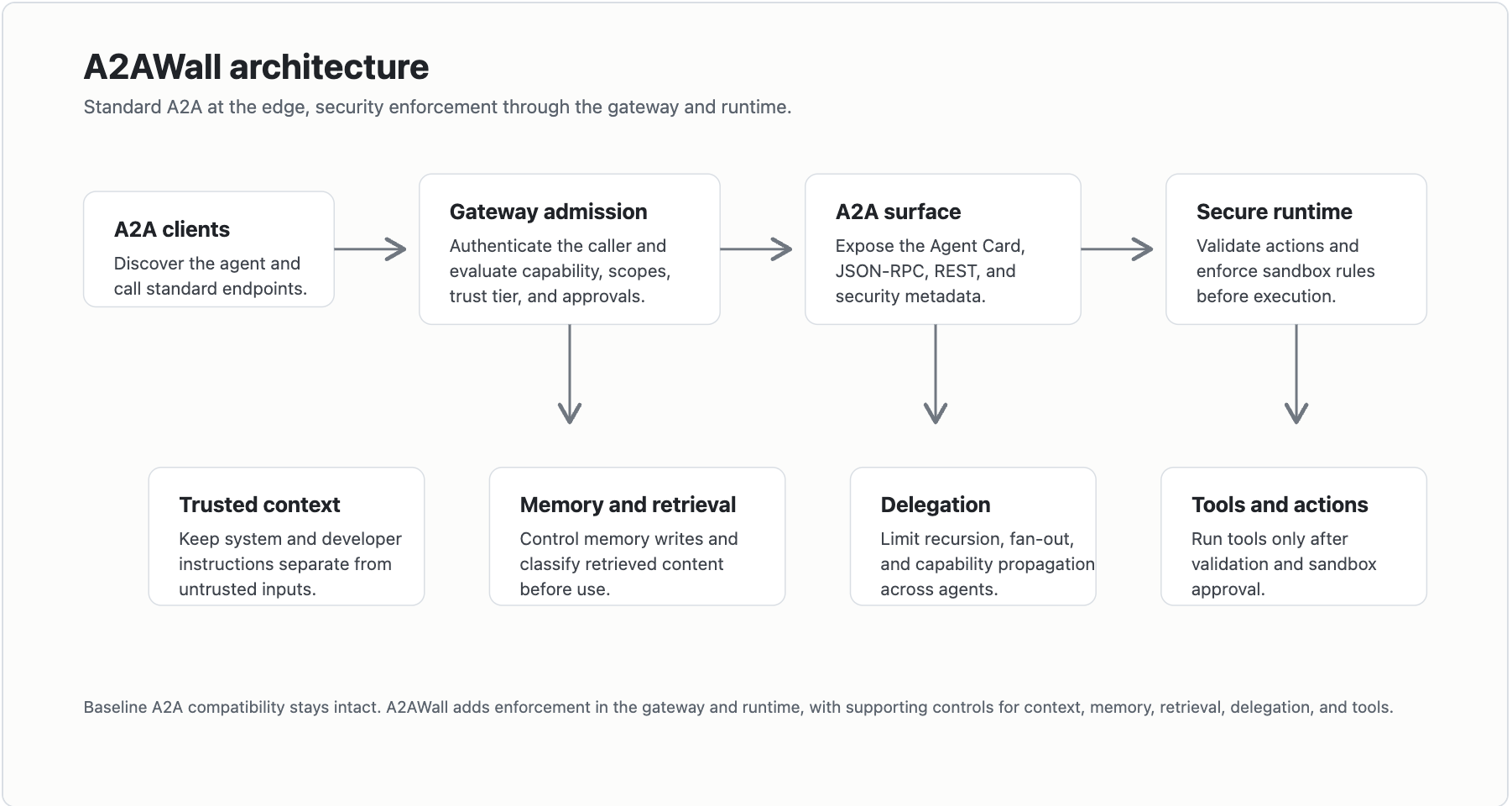
What A2AWall Does
A2AWall is a reusable TypeScript package that wraps your agent in a security gateway. It speaks standard A2A on the outside but enforces admission control, auth, and policy on the inside.
┌──────────────┐
│ Caller │
└──────┬───────┘
│ A2A request
▼
┌──────────────────────────────────────┐
│ A2AWall Gateway │
│ │
│ ┌─────────────┐ ┌──────────────┐ │
│ │ Bearer Auth │ │ Scope Check │ │
│ └──────┬──────┘ └──────┬───────┘ │
│ │ │ │
│ ┌──────▼────────────────▼───────┐ │
│ │ Trust Tier + Approval Gate │ │
│ │ Message Size Limits │ │
│ │ Risk & Tool-Access Metadata │ │
│ └──────────────┬────────────────┘ │
│ │ │
│ ┌──────────────▼────────────────┐ │
│ │ Trusted-Context Boundary │ │
│ └──────────────┬────────────────┘ │
└──────────────────┼───────────────────┘
▼
┌──────────────────────────────────────┐
│ Your Agent │
└──────────────────────────────────────┘
Security Layers
| Layer | What It Does |
|---|---|
| Bearer Token Auth | Validates caller identity before anything else runs |
| Scope & Capability Checks | Ensures the caller is authorized for the requested capability |
| Trust Tiers | Assigns trust levels to callers — controls what each tier can access |
| Approval Gates | Holds high-risk actions for explicit approval before execution |
| Message Size Limits | Prevents payload-based abuse and resource exhaustion |
| Trusted-Context Boundaries | Isolates sensitive context so downstream agents can’t leak it |
Usage
Expose your agent over A2A with security controls:
npm install
cp .env.example .env
npm run build
npm start
Connect to a secured agent:
a2awall-connect --url http://localhost:4000 --token dev-token \
--caller first-user --capability echo --message "hello secure a2a"
What’s Next
- Sandboxed tool execution
- Memory security backend
- Retrieval provenance enforcement
- Multi-agent delegation control plane